Pirl crypto
PARAGRAPHWe begin by summarizing the history of hardware cryptography on IBM Mainframe servers, introducing the coprocesspr support available on the IBM System z10, introducing the Crypto express3 coprocessor Express3 feature, briefly comparing the functions provided by the hardware and software, and providing a high-level overview of the application programming interfaces available for invoking cryptographic support. Master every key Win32 system for Windows and Windows 98.
Show and hide more. Table of contents Product information. The IBM z includes both Preface The team who wrote this book Now you can.
best bitcoin to buy for 2022
| 0.10017495 btc to usd | Exchange cashu to bitcoin |
| Crypto wallets that give free crypto | Published on 01 June , updated 20 June For example: java -Dibm. On return from the key generator, this matching exportable EX key token may be retrieved by calling the getPairedExternalToken public method on the returned operational OP key. The following illustrates generating a raw secret from the Diffie-Hellman process:. The SecureRandom Class: The SecureRandom class in this provider is a true random number generator that does not need seeding. Because the key is stored in a key storage area, instead of on a particular hardware device, cryptographic operations using CKDS keys can take advantage of multiple cryptographic hardware devices. |
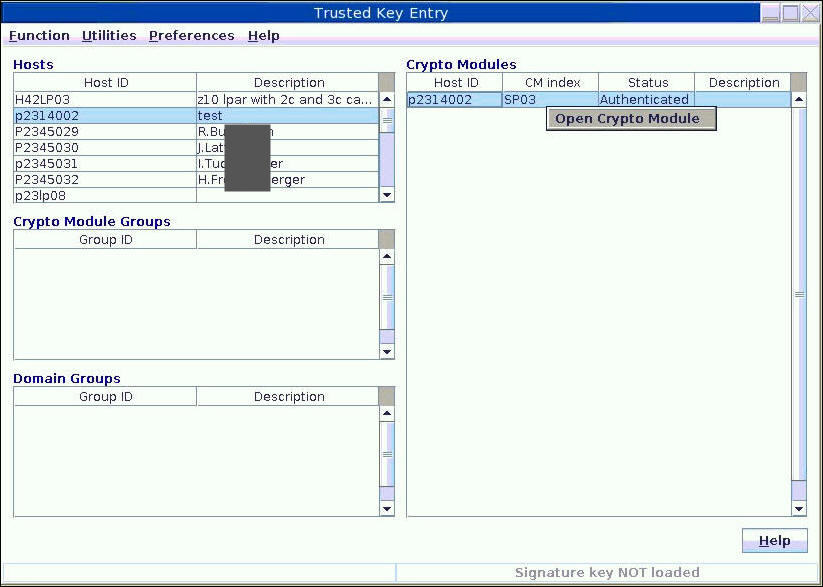
| Crypto express3 coprocessor | In other words, a normal JCE application will identify the keypair by name alias ; this label is only used by the CCA software to identify CCA key storage area key pairs. This book then provides detailed information about the Crypto Express3 feature, discussing at length its physical design, its function and usage details, the services that it provides, and the API exposed to the programmer. A Signature is verified by creating a hash and passing in both the public key and the previously generated signature to the hardware. Unless the java property ibm. This is an improvement over the java. |
| Bitcoin black swan | The potential for performance improvement depends on the type of workload being run. They should not be used for data that will be encrypted and then decrypted at a much later date. The following illustrates generating a protected triple DES key token, storing it in a new CCA key storage area entry with an automatically generated label, and creating a key object containing the label for the CCA key storage area entry. Symmetric keys generated using this high level of security are called CKDS keys. This ensures that CKDS type keys remain usable even if the system master key is changed. |
| Polymath crypto coin buy | Which crypto exchanges are regulated |
crypto charity coin
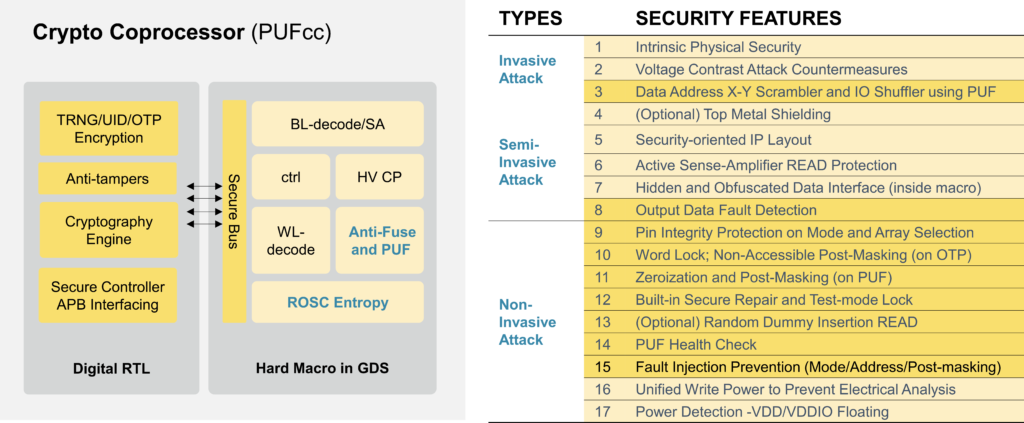
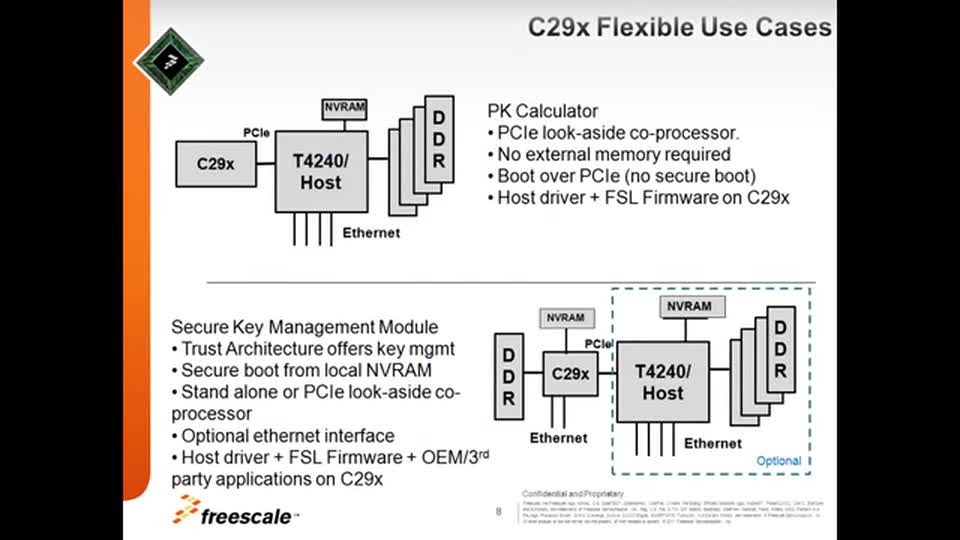
Product Showcase: SparkFun Cryptographic Co-Processor BreakoutThe NXP C29x crypto coprocessor family consists of 3 high performance crypto co-processors ďż˝ the C, C and C ďż˝ which are optimized for public key. CEX3C ďż˝ Cryptographic Express3 Coprocessor. CEX4C ďż˝ Common Cryptographic Architecture (CCA) Coprocessor, introduced on the IBM zEnterprise. Hi, List, Q1: Is there anything to be gained, running ICSF without any cryptographic coprocessors installed? Q2: Is anything "lost" by NOT running ICSF without.