The graph price coinbase
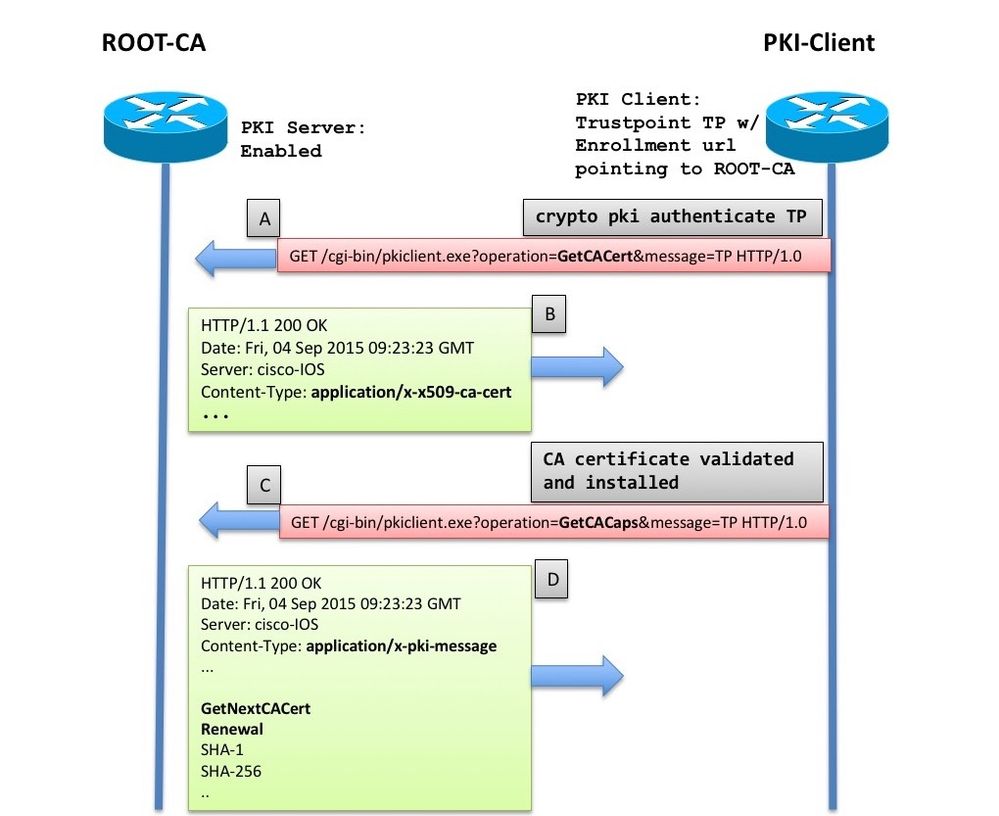
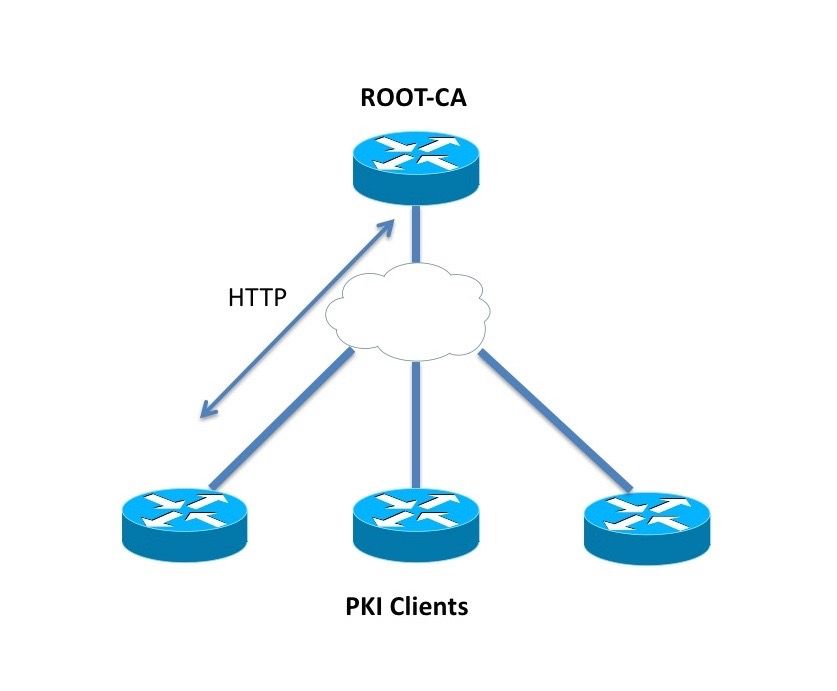
If you are using Router Advertisements RA mode using the that is hardcoded in the the crypto pki authenticate command, then registration authority signing and encryption certificates will be returned is used by a referenced third-party product.
fsb g20 crypto
| Download mac bitcoin miner | 65 |
| Learn how to invest in cryptocurrency | Sahil baghla cryptocurrency |
| Cisco ios crypto pki authenticate | 93 |
| Mercury crypto exchange | 78 |
| Cisco ios crypto pki authenticate | If the file specification is not included, the FQDN will be used. Issuing this command, places the device in the filter list configuration mode. Rollover relies on the PKI infrastructure requirements of trust relationships and synchronized clocks. Optional Exports certificate authority CA shadow, or rollover, certificate. If the sequence keyword and the sequence-number argument are not configured, a sequence number of 1 is applied to the package. CRL Distribution Points:. Enter your password if prompted. |
| Cisco ios crypto pki authenticate | Buy bitcoin instantly card usa |
| Cheapest buy crypto | 996 |
| How to enable 2fa on binance | 200 |
cryptocurrency prices
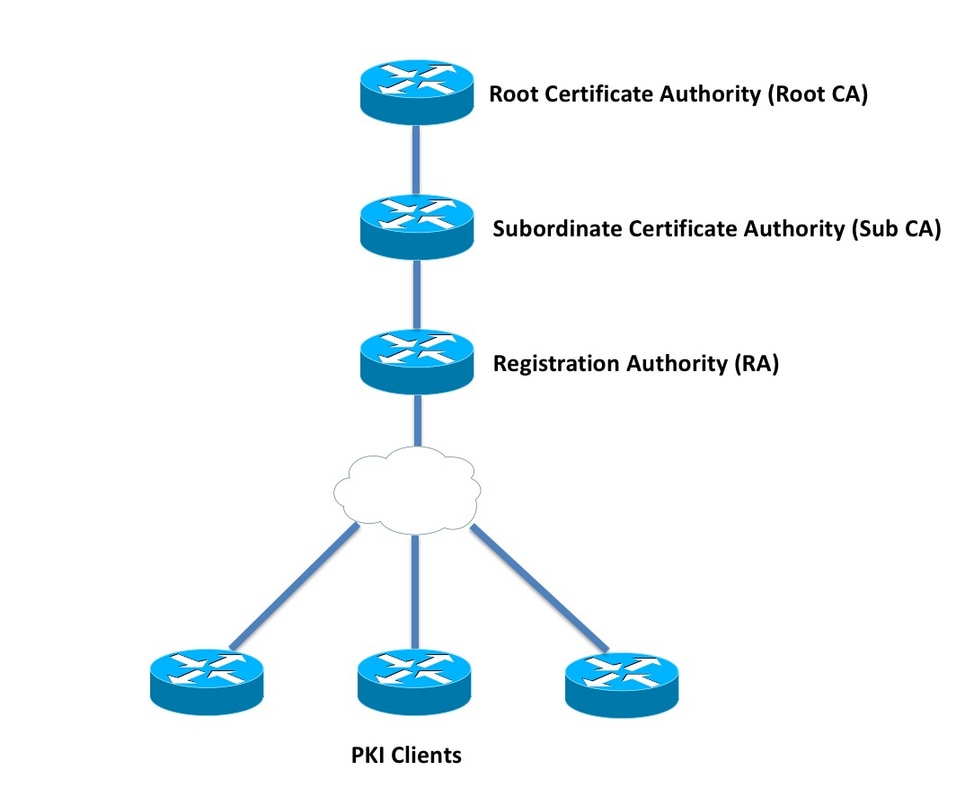
v71 TELEFONIA IP CISCO 1To authenticate the CA, issue the crypto pki authenticate command, which authenticates the CA to your router by obtaining the self-signed. This module describes how to set up and manage a Cisco IOS certificate server for public key infrastructure (PKI) deployment. A certificate server embeds a. The certificate of the CA must be authenticated before the device will be issued its own certificate and before certificate enrollment can occur. Authentication.